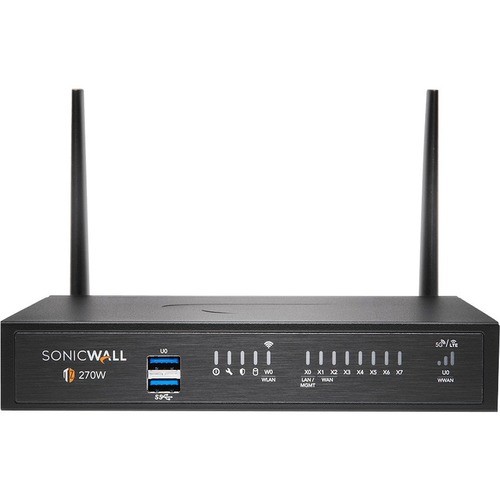
SonicWall TZ270W Network Security/Firewall Appliance - Intrusion Prevention - 8 Port - 1000Base-T - Gigabit Ethernet - 256 MB/s Firewall Throughput - Wireless LAN IEEE 802.11ac - AES (192-bit), DES, MD5, AES (256-bit), 3DES, AES (128-bit), SHA-1 - 8 02-SSC-8444
02-SSC-8444 | Sonicwall®
Part Number: 02-SSC-8444
Condition: New
In Stock: 13
Real time availability 
Product Specifications
SonicWall TZ270W Network Security/Firewall Appliance - Intrusion Prevention - 8 Port - 1000Base-T - Gigabit Ethernet - 256 MB/s Firewall Throughput - Wireless LAN IEEE 802.11ac - AES (192-bit), DES, MD5, AES (256-bit), 3DES, AES (128-bit), SHA-1 - 8 02-SSC-8444
EXISTING SNWL CUST TRADE UP - TZ270 WIRELESS-AC APPLIANCE ONLY
Manufacturer Part Number: 02-SSC-8444
EXISTING SONICWALL CUSTOMER TRADEUP TZ270 WIRELESS-AC (Appliance Only). This Gen 7 Upgrade Partner Promotion is a SonicWall replacement promotion. This is NOT for competitive replacement. PROMOTIONAL PRODUCTS CAN ONLY BE REGISTERED WITH SERIAL NUMBER ENTRY OF AN ELIGIBLE REPLACEMENT PRODUCT. Upgrades must fit within the existing Secure Upgrade Matrix. Any misuse of this promotion will require RMA.
MANUFACTURER NAME: Sonicwall
MANUFACTURER PART NUMBER: 02-SSC-8444
UPC EAN CODE: 758479284444
LANGUAGE: EN
MARKET:US
| General Information: | |
The latest SonicWall TZ series, are the first desktop form factor next-generation firewalls (NGFW) with 10 or 5 Gigabit Ethernet interfaces. The series consist of a wide range of products to suit a variety of use cases. | |
| Manufacturer | SonicWall Inc. |
| Manufacturer Part Number | 02-SSC-8444 |
| Manufacturer Website Address | http://www.sonicwall.com |
| Brand Name | SonicWall |
| Product Series | TZ |
| Product Model | TZ270W |
| Product Name | TZ270W Network Security/Firewall Appliance |
| Product Type | Network Security/Firewall Appliance |
| Product UPC | 758479284444 |
| Technical Information: | |
| Functionality | Intrusion Prevention |
| Firewall Protection Supported | Stateful Packet Filtering
Reassembly-free Deep Packet Inspection Distributed Denial of Service (DDoS) DNS Security TLS Decryption SSL Decryption SSL Inspection Malware Protection Gateway Antivirus Application Control URL Filtering Web Content Filtering Anti-spyware Intrusion Prevention Deep Inspection Firewall Anti-spam Zero Day Event Dead Peer Detection Secure IPsec VPN Connectivity Policy Based Filtering Data Loss Prevention Data Theft Protection Botnet Filtering Cloud Sandboxing Real-Time Deep Memory Inspection (RTDMI) SSH Decryption SSH Inspection TLS Inspection Advanced Threat Protection |
| Firewall Throughput | 2 Gbit/s |
| Encryption Standard | AES (192-bit)
DES MD5 AES (256-bit) 3DES AES (128-bit) SHA-1 |
| Interfaces/Ports: | |
| Total Number of Ports | 8 |
| USB | Yes |
| Number of Network (RJ-45) Ports | 8 |
| Media & Performance: | |
| VPN Throughput | 93.75 MB/s |
| Network & Communication: | |
| Ethernet Technology | Gigabit Ethernet |
| Network Standard | 1000Base-T |
| Wireless Specifications: | |
| Wireless LAN | Yes |
| Wireless LAN Standard | IEEE 802.11ac |
| Management & Protocols: | |
| Manageable | Yes |
| Power Description: | |
| Frequency | 50 Hz
60 Hz |
| Physical Characteristics: | |
| Form Factor | Desktop |
| Height | 1.8" |
| Width | 7.5" |
| Depth | 5.3" |
| Weight (Approximate) | 1.81 lb |
| Miscellaneous: | |
| Environmentally Friendly | Yes |
| Environmental Compliance | Waste Electrical and Electronic Equipment Directive (WEEE)
Restriction of Hazardous Substances (RoHS) Registration, Evaluation, Authorization and Restriction of Chemicals (REACH) |
| Country of Origin | Taiwan |
| TAA Compliant | Yes |
Questions and Answers
Questions and Answers | Ask CompSource |
Shipping / Returns
Shipping
Ground =
FREE
(EST. Arrival Date between
Wed.Dec.25 - Mon.Dec.30)
Two Day Air = $28.00
(EST. Arrival Date on Wed.Dec.25)
Standard One Day = $49.00
(EST. Arrival Date on Tue.Dec.24 after 3PM)
Priority = $75.00
(EST. arrival Date on Tue.Dec.24 in the AM)
U.S Mail Priority (AA,AE,AP only) = $38.50
FedEx International Economy (Canada only) = $88.00
Shipping dates are best estimates based on product location and may vary with holidays.
If product requires trucking, additional fees may apply.
* Some destinations are subject to Applicable State/Duty Taxes
Returns
CompSource realizes that every product may have different return guidelines. Please see the policy below regarding this item.
This Product Has Limited Exchange Privileges.
Please call for return guidelines.
For support on this product, please contact Sonicwall. 888.777.1476 WWW.SONICWALL.COM
Sonicwall Company's Information
Click Sonicwall for all products
Local #: (408)745-9600
Toll Free #: 888.777.1476
Site: WWW.SONICWALL.COM
Product Reviews
Overall Rating | Write a Review
|
|
Best Sellers
More Best Sellers
Rebates
More Rebates
Learn more about Network Security & Firewalls
Switches, routers, and wireless access points
Switches, routers, and wireless access points perform very different functions in a network.
A computer network, or data network, is a digital telecommunications network which allows nodes to share resources. In computer networks, computing devices exchange data with each other using connections (data links) between nodes These data links are established over cable media such as wires or optic cables, or wireless media such as WiFi.Switches
Switches are the foundation of most business networks. A switch acts as a controller, connecting computers, printers, and servers to a network in a building or a campus.
Switches allow devices on your network to communicate with each other, as well as with other networks, creating a network of shared resources. Through information sharing and resource allocation, switches save money and increase productivity.
There are two basic types of switches to choose from as part of your networking basics: managed and unmanaged.
- An unmanaged switch works out of the box but can't be configured. Home-networking equipment typically offers unmanaged switches.
- A managed switch can be configured. You can monitor and adjust a managed switch locally or remotely, giving you greater control over network traffic and access.
Routers
Routers connect multiple networks together. They also connect computers on those networks to the Internet. Routers enable all networked computers to share a single Internet connection, which saves money.
A router acts a dispatcher. It analyzes data being sent across a network, chooses the best route for data to travel, and sends it on its way.
Routers connect your business to the world, protect information from security threats, and can even decide which computers receive priority over others.
Beyond those basic networking functions, routers come with additional features to make networking easier or more secure. Depending on your needs, for example, you can choose a router with a firewall, a virtual private network (VPN), or an Internet Protocol (IP) communications system.
Access points
An access point* allows devices to connect to the wireless network without cables. A wireless network makes it easy to bring new devices online and provides flexible support to mobile workers.
An access point acts like an amplifier for your network. While a router provides the bandwidth, an access point extends that bandwidth so that the network can support many devices, and those devices can access the network from farther away.
But an access point does more than simply extend Wi-Fi. It can also give useful data about the devices on the network, provide proactive security, and serve many other practical purposes.
*Access points support different IEEE standards. Each standard is an amendment that was ratified over time. The standards operate on varying frequencies, deliver different bandwidth, and support different numbers of channels.
Wireless networking
Wireless networking is a method by which homes, telecommunications networks and business installations avoid the costly process of introducing cables into a building, or as a connection between various equipment locations.Firewall
And possibly the most important aspect of networking is security and Firewall!What is a Firewall?
A firewall is a network security device that monitors incoming and outgoing network traffic and decides whether to allow or block specific traffic based on a defined set of security rules.
Firewalls have been a first line of defense in network security for over 25 years. They establish a barrier between secured and controlled internal networks that can be trusted and untrusted outside networks, such as the Internet.
A firewall can be hardware, software, or both.
CompSource will educate and help make this process enjoyable and easy.
Whether you're planning on using your network for basic home tasks or enterprise level security. You can tell our trained sales professionals your needs, and we�ll make custom recommendations to suit your specifications and budget. Our reps have extensive knowledge and love to share. We educate, not sell, CompSource makes sure you buy what you need and not waste money on what you don't. As with every decision we never push, it's up to you when, and if you make a purchase.
CompSource has a great technical staff that can help with a solution for your exact needs.
Chat with us or give our professionals a quick phone call (800)-413-7361.
Excellent. My purchase was delivered on time and in good condition. I did contact CompSource, asking for tracking information, which I received immediately. That information was absolutely accurate. I am very pleased and recommend CompSource to others based on their good pricing and customer service. BFullerMore Reviews